Central to this is safeguarding and securing the overall system and procedural flows. Mining and Oil & Gas players must adhere to strict standards – not only self-imposed standards but also global, in country, and within the industry itself – to make their operations secure, safe and environmentally sound. As companies transition to more connected operations, policies and procedures for data access and management are more critical than ever.
In the mining and refining context, Process Control Network’s (PCN or process control systems - PCS) power critical operational components - providing deep and sometimes complex process information, in a simple and logical format for decision making. Merging processing and corporate infrastructures can help with system improvement and optimization by highlighting key areas for production improvements, shining a light on under-performing units and allowing for product quality improvements.
The use of advanced PCN procedures can not only increase profit margins, but also reduce emissions, minimise or remove safety and security issues and maximise the lifespan and maintenance regimes of operating equipment.
As the level of digitisation increases, so too does the attack surface
Process Control Networks are complex in design and implementation because they integrate with a range of corporate and industrial components. PCN's perform sensitive and vital tasks for managing and handling critical infrastructure. It’s imperative to implement security in these systems because they are targets for cyber-attacks.
A successful and coordinated cyber-attack can incur massive damage to an organisation's infrastructure. But it doesn’t even have to be a planned attack, it could be accidental. Outages, a safety breach, downtime, loss of production, environmental impacts could all be caused by accident.
If there is an outage or a safety incident how would this impact your company?
Your team, reputation, partnerships, shareholders, customers?
Digital security was important 10 years ago but getting on the front foot is even more important today. Traditionally, industrial equipment was directly connected to the servers or devices which were controlling or monitoring it. PCN’s were not designed to be connected to the internet and digital security was largely not even considered during development and design.
This means, without a PCN plan, processing plants could find themselves in a vulnerable situation where:
- Systems are unsupported/outdated/insecure
- Internet connectivity leads to an increased attack surface
- Authentication/authorization is inadequate
- Monitoring is inadequate
"Potentially you could have someone sitting in front of an office desk that could affect production, purely by having incorrect controls set up that can impact the success or failure of a processing plant."
Policies and Procedures are Key
Refineries, mines - or any processing plant - have multiple layers of data and complexity. The data that can control the success or failure of the plant needs to be safe, secure and accessible, for the right people at the right time. The integration of IT and OT means digital architectures must encompass a holistic perspective – leveraging a model based on the Group Practices and Guide Notes for PCN communications and infrastructure.
Many refineries, mines and processing plants are embarking on a review of their PCN, and need to start the process by looking at their current state with reviews such as:
- What is in the network?
- What software/hardware exists?
- What documentation and processes already exist?
- What physical separation of networks exist? (physical access to the hardware and the logical access between networks)
- Are existing policy and procedures in place to manage the physical separation of the networks?
In addition, refineries and mining sites must follow industry standards and should have their own internal policies and procedures set up to ensure clear demarcation zones for data layers:
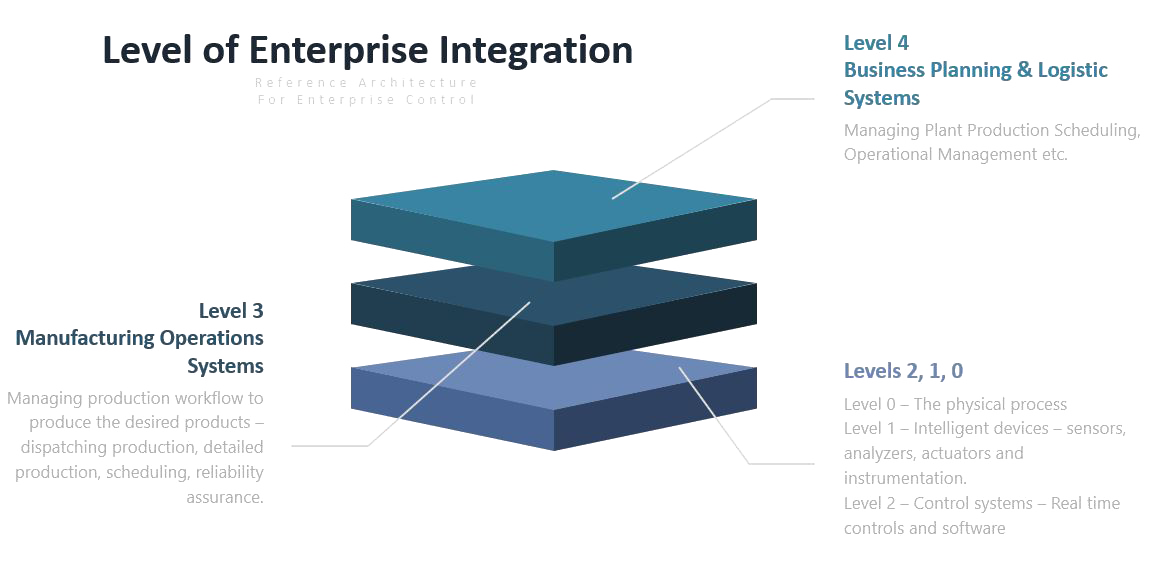
In the diagram:
Level 4 shows the Business Planning and Logistics Network layer
Level 3 shows the Demilitarized Zone (DMZ) network – often referred to as the Process Information Network or PIN, is the zone that connects the office network and the production network. It controls the data flow but doesn’t control the network.
Level 2,1, 0 house the Process Control Network is the actual production data layer that needs to be accessed by the business for decisions.
* PERA is a reference architecture that can model the enterprise in multiple layers and in multiple stages of the architectural life cycle. https://www.tandfonline.com/doi/full/10.1080/09537280310001647841
When reviewing and securing your PCN, make sure you (or the partner company who helps you):
- Inherently knows the rules and Industry Standards for refineries, mining and/or processing plants in general.
- Understands what is required for physical and logical segregation.
- Can identify risks, issues and areas of improvement based on their skill set and their refining, mining and/or processing plant experience.
- Can pull in all the stakeholders to make sure the project runs successfully.
Conclusion
It’s imperative to implement security in PCN's as they perform sensitive and critical tasks for managing and handling critical refinery, mining and processing plant infrastructure. Along the way to securing your PCN architecture, risks and opportunities for improvements need to be identified and issues pinpointed - covering everything from the logical access to the data via software, to the physical protection of the machines managing the production data.
Most PCN system cyber-attacks can be mitigated by implementing available frameworks, legislation and guidelines. If done correctly, your refinery, mine or processing plant will be able to drive:
- Improved process safety (earlier identification of problems, process watchdog)
- Improved operator effectiveness (focuses on key operating parameters)
- Reduced (downstream) unit variability (fewer process upsets)
- Better process information (increased process understanding)
- Reducing the risk of safety incidents
- Reduced loss of production/loss of control whether it’s by accident/inadvertent actions by people just because they can (access levels unknown in an organisation
Thanks to Thomas Woerner, Subject Matter Expert and Jen Wright, blog author for collaborating on this topic.
The Digital Chemistry between Strategies, Tactics & Operations
Denver’s Digital Maturity Assessment (DMA) Case Study for a Major Chemical Manufacturer in The Mining Industry.
Read moreThe Difference of a Red Cap
Denver's Principal IT/OT Advisors, Marco Van Staden, detailed his account as a junior engineer in South Africa.
Read blogUp-time and Reliability with Better Asset Maintenance
Have you ever considered the bottom line impact of running a less than optimal asset maintenance regime? "Under servicing" can have dire impacts on up-time but so can "over servicing" where the asset life cycle management is either not understood, or not visible to those accountable.
Read blog